New Delhi, June 14, 2022 - Check Point Research (CPR) exposes an Iranian spear-phishing operation targeting high-profile Israeli and US executives. The attackers hijacked emails of senior people in Israel and then used it to target other high-level officials to steal personal information. Targets have included former Israeli Foreign Minister, Tzipi Livni, the former US Ambassador to Israel, former Major General of the IDF, and three others. In addition, the attackers hijacked existing email exchanges and swapped emails to new ones, pretending to be someone else, to trick their targets into speaking to them. CPR believes the goal of the operation is to steal personal information, passport scans and access email accounts. CPR’s findings come at a time of rising tensions between Israel and Iran, where former attempts by Iran to lure Israeli targets via email have occurred.
- Operation dates to at least December 2021
- Attackers impersonated email accounts of trusted contacts in the format of joe.doe.corp@gmail.com
- Findings suggest the operation is connected to the Iran-attributed Phosphorus APT group
Check Point Research (CPR) has exposed an Iranian spear-phishing operation targeting high-profile Israeli and US executives. As part of their operations, the attackers take over existing accounts of the executives and create fake impersonating accounts to lure their targets into long email conversations. CPR believes the goal of the operation is to steal personal information, passport scans, and access to email accounts. CPR sees that the operation dates to at least December 2021 but assumes earlier.
High profile targets include:
- Tzipi Livni - former Foreign Minister and Deputy Prime Minister of Israel
- Former Major General who served in a highly sensitive position in the IDF
- Chair of one of Israel’s leading security think tanks
- Former US Ambassador to Israel
- Former Chair of a well known Middle East research center
- Senior executive in the Israeli defense industry
Attack Methodology
- The attacker takes over a real e-mail account of a frequent contact of the target
- The attacker proceeds to hijack an existing email conversation
- The attackers then open a fake email to impersonate the contact of the target, mostly in the format of joe.doe.corp@gmail.com.
- The attackers continue the hijacked conversation from the fake email and exchanges at least several emails with the target
- Some of the emails include a link to a real document that is relevant to the target. e.g, invitation to a conference or research / phishing page of Yahoo/ link to upload document scans
Example Emails: Tzipi Livni, Former Israeli Foreign Minister
Livni was approached via email by someone impersonating a well-known former Major General in the IDF who served in a highly sensitive position. The email was sent from his genuine email address which had previous correspondence with her in the past. The email contained a link to a file which the attacker requested her to open and read. When she delayed doing so, the attacker approached her several times asking her to open the file using her email password. This prompted her suspicions. When she met the former Major General and asked him about the email, it was confirmed that he never sent such an email to her.
Figure 1. Email to Tzipi Livni on Day 1
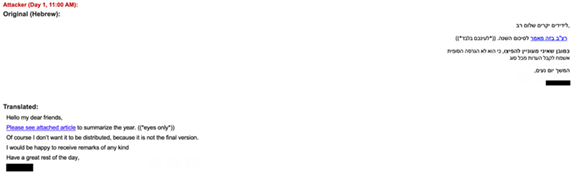
Figure 2. Email to Tzipi Livni on Day 6

Attribution
CPR believes that the threat actors behind the operation are an Iranian-backed entity. Evidence points to a possible connection of the operation to the Iran-attributed Phosphorus APT group. The group has a long history of conducting high-profile cyber operations, aligned with the interest of the Iranian regime, as well as targeting Israeli officials.
Quote: Manish Alshi, Head of Channels and Growth Technologies - India & SAARC, Check Point Software Technologies:
“We have exposed Iranian phishing infrastructure that targets Israeli and US public sector executives, with the goal to steal their personal information, passport scans, and steal access to their mail accounts.
We have solid evidence that it started at least from December 2021 ; but we assume that it started earlier. The most sophisticated part of the operation is the social engineering. The attackers use real hijacked email chains, impersonations to well-known contacts of the targets and specific lures for each target. The operation implements a very targeted phishing chain that is specifically crafted for each target. In addition, the aggressive email engagement of the nation state attacker with the targets is rarely seen in the nation state cyber-attacks. CPR will continue to monitor the operation.”
About Check Point Software Technologies Ltd.
Check Point Software Technologies Ltd. is a leading provider of cyber security solutions to corporate enterprises and governments globally. Check Point Infinity´s portfolio of solutions protects enterprises and public organizations from 5th generation cyber-attacks with an industry leading catch rate of malware, ransomware and other threats. Infinity comprises three core pillars delivering uncompromised security and generation V threat prevention across enterprise environments: Check Point Harmony, for remote users; Check Point CloudGuard, to automatically secure clouds; and Check Point Quantum, to protect network perimeters and datacenters, all controlled by the industry’s most comprehensive, intuitive unified security management. Check Point protects over 100,000 organizations of all sizes.
*Disclamier: "The pages slugged ‘Press Release’ are equivalent to advertisements and are not written and produced by Industry Outreach Magazine journalists/Editorial." We do not hold any copyrights towards the content or image. Image source: Newswire







